Kerberos V5 Installation Guide. Mar 19, 2021 The keytab file keeps the names of Kerberos principals and the corresponding encrypted keys. Now let’s take a look at how our Support Engineers create a keytab file. First, we create a service account in AD and set a known password for it.
- Create Keytab For Kerberos Authentication In Linux - Tech Jogging
- Generate Keytab File Kerberos
- Generate Keytab File From Active Directory
- Generate Keytab File Windows
- Cached
To create a keytab file: On the domain controller server, create a user account named control- in the Active Directory Users and Computers snap-in. If you want to use the AES256-SHA1 encryption algorithm, do the following in the Active Directory Users and Computers snap-in: Open the properties of the created account. Importing the keytab file to the firewall Step 1: Once you have the keytab file generated, you can import it to the authentication profile used by GlobalProtect or Captive Portal. Step 2: After completing the above steps, authentication with the firewall should happen without any user intervention, and you should see the service ticket using.
In order to configure and enable Kerberos authenticator on Squid proxy navigate to UI / Squid Proxy / Auth / Active Directory and click the Kerberos tab.
You will need to provide the following information.
Kerberos realm
This is usually the UPPERCASE letters of your Active Directory domain. For example.lan domain it will be EXAMPLE.LAN. Please note that Kerberos realm is always uppercase. Click the wizard button next to the field to try autodetection based on your DNS and DHCP settings.
Service Principal Name
The Service Principal Name (SPN) - is the Kerberos principal that will be used by the connecting browsers for authentication. It is usually constructed from the FQDN of the proxy and Kerberos realm automatically. For example, HTTP/proxy.example.lan@EXAMPLE.LAN. Click the wizard button next to the field to try autodetection based on your DNS and DHCP settings.
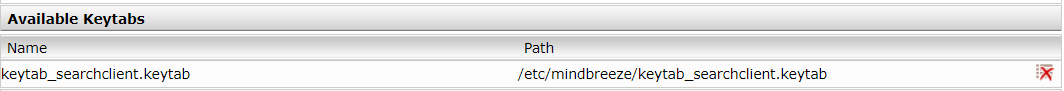
KeyTab for SPN
Here you must specify the keytab file that contains entries required to do the Kerberos authentication.
Important

Please note, designated squid@example.lan user we created on the previous step, Service Principal Name and KeyTab file are three closely related entities. SPN is mapped to user squid@example.lan. Keytab is generated from both SPN and squid@example.lan user as follows.
Login as Administrator to your Domain Controller
Start the elevated Command Prompt
Change to disk C:
Run the following command
The command will make C:krb5.keytab file and the output will look like the following.

Danger
Create Keytab For Kerberos Authentication In Linux - Tech Jogging
If you already have this SPN mapped to another user as indicated in the article Check the SPN is Mapped to One User Only key tab generation may fail with the following error.
Now set Enable Kerberos authenticator checkbox, specify C:krb5.keytab in the key tab browse button, set the SPN and click Save Changes.
After sucessful upload the application will perform various validation of the keytab, and will try to perform Kerberos authentication to the configured domain controller by running a series of Kerberos commands as indicated on Troubleshooting Squid Active Directory Integration. Output of these commands is shown on the Kerberos configuration page.
Important
Technical information: Admin UI generates correct Kerberos conf file in /opt/websafety/etc/krb5.conf based on the uploaded keytab, SPN and Kerberos realm. This configuration file is later used by the Kerberos authenticator to initialize Kerberos libraries. That is why it is possible to leave the default /etc/krb5.conf empty.
The generated Kerberos configuration file will usually look like:
Important
Generate Keytab File Kerberos
More technical information: excerpt from microsoft’s documentation for Active Directory … unlike Kerberos principal names, Windows account names are not multipart. Because of this, it is not possible to directly create an account of the name HTTP/proxy.example.lan in the Active Directory. Such a principal instance can be created through the service principal name mappings…
Warning
There should be ONLY one user mapped to a given SPN. If you have two or more different Active Directory users mapped to one SPN - Kerberos authentication will ALWAYS FAIL. For more information see blog entry at https://blogs.technet.microsoft.com/askds/2008/06/09/kerberos-authentication-problems-service-principal-name-spn-issues-part-2.
-->Applies to: Windows Server 2022, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, Windows Server 2012
Configures the server principal name for the host or service in Active Directory Domain Services (AD DS) and generates a .keytab file that contains the shared secret key of the service. The .keytab file is based on the Massachusetts Institute of Technology (MIT) implementation of the Kerberos authentication protocol. The ktpass command-line tool allows non-Windows services that support Kerberos authentication to use the interoperability features provided by the Kerberos Key Distribution Center (KDC) service.
Syntax
Parameters
| Parameter | Description |
|---|---|
/out <filename> | Specifies the name of the Kerberos version 5 .keytab file to generate. Note: This is the .keytab file you transfer to a computer that isn't running the Windows operating system, and then replace or merge with your existing .keytab file, /Etc/Krb5.keytab. |
/princ <principalname> | Specifies the principal name in the form host/computer.contoso.com@CONTOSO.COM. Warning: This parameter is case-sensitive. |
/mapuser <useraccount> | Maps the name of the Kerberos principal, which is specified by the princ parameter, to the specified domain account. |
/mapop {add|set} | Specifies how the mapping attribute is set.
|
{-|+}desonly | DES-only encryption is set by default.
|
/in <filename> | Specifies the .keytab file to read from a host computer that is not running the Windows operating system. |
/pass {password|*|{-|+}rndpass} | Specifies a password for the principal user name that is specified by the princ parameter. Use * to prompt for a password. |
| /minpass | Sets the minimum length of the random password to 15 characters. |
| /maxpass | Sets the maximum length of the random password to 256 characters. |
/crypto {DES-CBC-CRC|DES-CBC-MD5|RC4-HMAC-NT|AES256-SHA1|AES128-SHA1|All} | Specifies the keys that are generated in the keytab file:
Note: Because the default settings are based on older MIT versions, you should always use the |
| /itercount | Specifies the iteration count that is used for AES encryption. The default ignores itercount for non-AES encryption and sets AES encryption to 4,096. |
/ptype {KRB5_NT_PRINCIPAL|KRB5_NT_SRV_INST|KRB5_NT_SRV_HST} | Specifies the principal type.
|
/kvno <keyversionnum> | Specifies the key version number. The default value is 1. |
/answer {-|+} | Sets the background answer mode:
|
| /target | Sets which domain controller to use. The default is for the domain controller to be detected, based on the principal name. If the domain controller name doesn't resolve, a dialog box will prompt for a valid domain controller. |
| /rawsalt | forces ktpass to use the rawsalt algorithm when generating the key. This parameter is optional. |
{-|+}dumpsalt | The output of this parameter shows the MIT salt algorithm that is being used to generate the key. |
{-|+}setupn | Sets the user principal name (UPN) in addition to the service principal name (SPN). The default is to set both in the .keytab file. |
{-|+}setpass <password> | Sets the user's password when supplied. If rndpass is used, a random password is generated instead. |
| /? | Displays Help for this command. |
Remarks
Services running on systems that aren't running the Windows operating system can be configured with service instance accounts in AD DS. This allows any Kerberos client to authenticate to services that are not running the Windows operating system by using Windows KDCs.
The /princ parameter isn't evaluated by ktpass and is used as provided. There's no check to see if the parameter matches the exact case of the userPrincipalName attribute value when generating the Keytab file. Case-sensitive Kerberos distributions using this Keytab file might have problems if there's no exact case match, and could even fail during pre-authentication. To check and retrieve the correct userPrincipalName attribute value from a LDifDE export file. For example:
Examples
Generate Keytab File From Active Directory
To create a Kerberos .keytab file for a host computer that isn't running the Windows operating system, you must map the principal to the account and set the host principal password.
Use the active directory User and computers snap-in to create a user account for a service on a computer that is not running the Windows operating system. For example, create an account with the name User1.
Use the ktpass command to set up an identity mapping for the user account by typing:
Note
You cannot map multiple service instances to the same user account.
Merge the .keytab file with the /Etc/Krb5.keytab file on a host computer that isn't running the Windows operating system.
Generate Keytab File Windows
